Viruses, trojans, software vulnerabilities, security issues
In the USA, they created a risk assessment system for AI algorithms
The National Institute of Standards and Technology (NIST), part of the U.S. Department of Commerce, which develops and tests technologies…
Researchers have taught AI to steal information from a monitor using radiation from an HDMI cable
A new study has found that hackers can use artificial intelligence to decipher electromagnetic radiation emanating from the cable that…
Secure Boot has been compromised on more than 200 PC models from major manufacturers, and this is just the beginning
Cybersecurity experts at Binarly have discovered that the Secure Boot protocol used in UEFI firmware has been compromised on more…
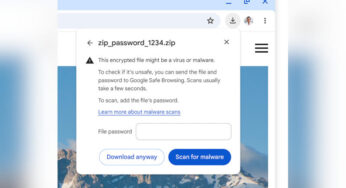
Chrome will be able to remotely check password-protected suspicious files, but you will have to provide the password to Google
Google has proposed an improved mechanism for detecting malware in the Chrome browser - now it will be possible to…
CrowdStrike outage costs Fortune 500 companies $5.4 billion
One in four Fortune 500 companies experienced outages during computer outages around the world last Friday caused by a botched…
A US company accidentally hired a North Korean hacker, who immediately began downloading viruses.
The American company KnowBe4, which specializes in cybersecurity issues, unwittingly hired a hacker from the DPRK, who tried to upload…
Vulnerability in Windows Hello allows hackers to bypass biometric security on business PCs
A vulnerability has been identified in the Windows Hello for Business (WHfB) authentication system that allows attackers to bypass the…
Alphabet failed to take over Wiz for $23 billion – the startup considered the proposed conditions humiliating
Cloud cybersecurity startup Wiz has refused a deal with Alphabet, the parent company of Google, which offered $23 billion for…
Systems affected by the CrowdStrike outage will take several weeks to recover
The massive outage, which affected about 8.5 million PCs running Microsoft Windows worldwide, although affecting just 1% of systems in…
Systems affected by the CrowdStrike outage will take several weeks to recover
The massive outage, which affected about 8.5 million PCs running Microsoft Windows worldwide, although affecting just 1% of systems in…