Viruses, trojans, software vulnerabilities, security issues
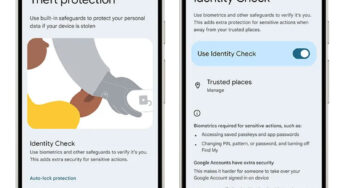
Google launches accounts through the print scanner on Android
Google has launched a new security feature for Android 15 that will help protect users' digital accounts from phone theft.…
A hole was found in Subaru’s software that made it possible to remotely unlock, start and monitor millions of cars.
Cybersecurity researchers Sam Curry and Shubham Shah discovered vulnerabilities in Subaru's Starlink infotainment system (not affiliated with SpaceX's satellite provider)…
Cloudflare once again repelled the largest DDoS attack in history – its power reached 5.6 Tbps
Cloudflare said it has repelled the largest distributed denial of service (DDoS) attack in history. The incident occurred at the…
Nvidia has patched software vulnerabilities for its GPUs that could allow data to be stolen and systems to crash.
Nvidia has announced fixes for several critical security vulnerabilities in its graphics drivers and virtual GPU management software. These vulnerabilities…
“Anonymity is not a fundamental right”: Europol said that messengers are obliged to disclose encrypted correspondence
Europol chief Catherine De Bolle called on big tech companies to cooperate with law enforcement on encryption issues, otherwise “they…
The average cost of a hacker attack has reached $20 thousand, but the attackers are not at a loss
The cost of a hacker attack using an encryption virus at the beginning of 2025 is on average $20 thousand,…
Hackers hacked AMD and stole secret data
Cybercriminals often include extortionists who demand ransom for valuable information stolen from companies. Apparently, AMD suffered a similar attack some…
Microsoft has released the largest Tuesday patch package for its software in recent years.
On Tuesday, January 14, Microsoft traditionally released a major package of security updates. This release was the largest in recent…
Groundhog Day on PC: Windows 10 update KB5048239 requires installing it again and again
#!MARKER#!Windows 10 update KB5048239, released on November 12, 2024, brings several improvements to the Windows Recovery Environment. According to numerous…
IPhone hacked via USB Type-C port because Apple was negligent in its security
At the end of last year, the annual Chaos Communication Congress event took place in Germany, bringing together information security…