Dangerous malware Perfctl was discovered, which managed to infect several thousand machines running Linux. The virus is distinguished by hidden mechanisms of operation, the ability to exploit a wide range of configuration errors, as well as a wide range of malicious actions that it can perform.

Image source: aquasec.com
Perfctl has been operational since at least 2021. It installs by exploiting more than 20,000 common configuration errors, meaning it could potentially target millions of Internet-connected machines, say cybersecurity experts at Aqua Security. The virus can also exploit the Apache RocketMQ system vulnerability numbered CVE-2023-33246 with a rating of 10 out of 10, which was closed last year. The malware was named Perfctl in honor of the component that deals with the hidden mining of cryptocurrencies – the name is made up of the names of the perf and ctl monitoring tools in Linux. The virus is characterized by using process or file names that are identical or similar to legitimate ones in Linux.
The virus disguises itself by resorting to many other tricks. It installs many of its components as rootkits – a special class of malware that can hide its presence from the operating system and administration tools. Other hidden Perfctl mechanisms:
- Pausing easily detectable activities when a user logs in;
- Using a Unix socket over Tor for external communication;
- Removing the binary after installation and then running it as a background service;
- Manipulations with the Linux pcap_loop process, preventing malicious traffic from being detected;
- Mesg error suppression, which prevents warnings from being issued at runtime.
The virus is able to remain on the infected machine after reboots or attempts to remove the main components. To do this, it can configure the environment at user logon time and boot before legitimate workloads, as well as copy itself from memory to multiple locations on disk. Perfctl not only mines cryptocurrency, but also turns the machine into a proxy server, for access to which hackers charge those who want to remain anonymous. In addition, the virus serves as a backdoor for the installation of malware of other families.
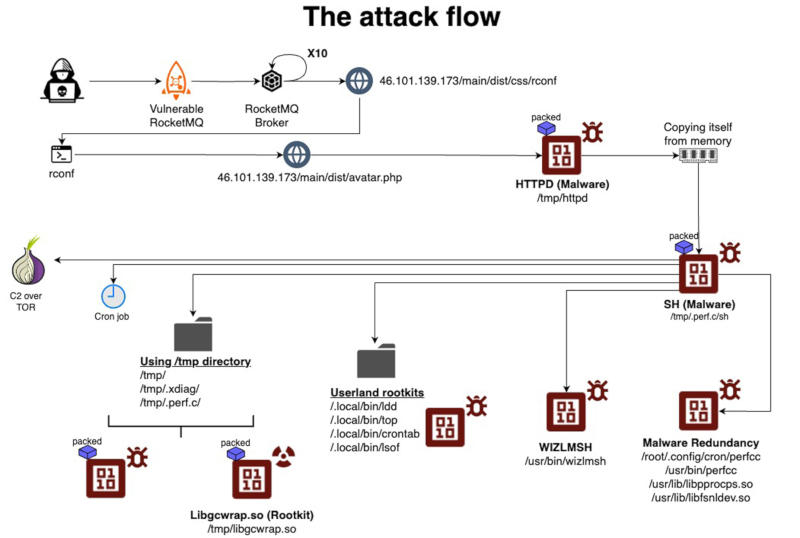
Taking advantage of a vulnerability or configuration error, the exploit code downloads the main payload from a server that was previously hacked and turned into a virus distribution channel – in one case, the payload was called “httpd”. Once executed, the file copies itself from memory to a new destination in the “/tmp” directory, runs it, deletes the original process and the loaded binary. Moving into the /tmp directory, the file is executed under a different name that imitates the name of a known Linux process – in one case called “sh” – from there it installs a local command and control process, and also attempts to gain root privileges by exploiting vulnerability CVE-2021-4043 of the open multimedia framework Gpac, which was closed in 2021.
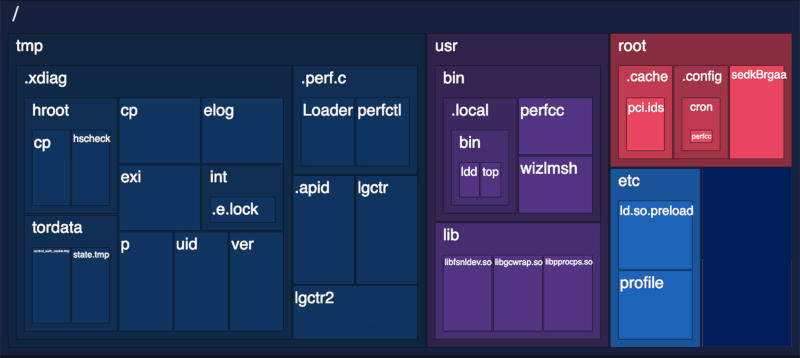
The virus continues to copy itself from memory to several other locations on the disk, using names that appear as normal system files. Next, many popular Linux utilities, modified to work as rootkits, and a miner are installed. To transfer control to a third-party operator, Perfctl opens a Unix socket, creates two directories and stores there the data that is necessary for its operation: host events, copy locations, process names, communication logs, tokens and additional information. All binary files are packaged, encrypted and deleted – this helps bypass security mechanisms and prevents attempts to reverse engineer the virus. Perfctl pauses by detecting the presence of the user in btmp or utmp files, and also blocks competing viruses to maintain control over the infected system.
The number of machines infected with Perfctl, according to experts, is measured in the thousands, but the number of vulnerable machines – which do not have the patch for CVE-2023-33246 installed or have an incorrect configuration – is estimated in the millions. Researchers have not yet calculated the volumes of cryptocurrency mined by secretive miners. There are many signs of infection, including unusual spikes in CPU usage or sudden system slowdowns, especially when idle. To prevent infection, it is necessary to close the CVE-2023-33246 vulnerability on the machine and correct the configuration errors pointed out by Aqua Security specialists.